| 1. |
Navigate to your Azure DevOps Organization page (e.g. http://dev.azure.com/contoso) |
| 2. |
Click on the shopping bag icon in the upper right corner next to your name, then click Manage extensions
|
| 3. |
If you do not see the Microsoft Security Code Analysis Extension listed under the Installed or
Shared with this account sections, please follow the How do I get the Microsoft Security Code Analysis
Extension shared with my account? section below |
| 4. |
Click the Microsoft Security Code Analysis extension |
| 5. |
On the subsequent page, Click Get it free
|
| 6. |
Choose the Azure DevOps Organization to install the extension on from the dropdown |
| 7. |
Click Install. Once it completes, you can Proceed to the account
|
Microsoft Security Code Analysis tasks work like any other Azure DevOps Build task. Here's how:
| 1. |
Edit your DevOps pipeline |
| 2. |
Click Add Task |
| 3. |
Click All or Utility under Add Tasks |
| 4. |
Find the secure development tool you would like to run (our tasks have a green security
shield icon) and click Add on the right hand side |
| 5. |
Use the 'Basic' input type to have the command line generated for you. Accept the defaults
or modify them (some tools require input that does not have a default). Or, |
| 6. |
Use the 'Command-Line' input type, and specify exact command-line arguments, if you are familiar
with the tool and its command-line parameters. |
|
Note that file or directory paths are relative to the root of your source repository, and
parameters specifying the output folder/files will be replaced with the common location
that we have defined on the build agent. |
| 7. |
Queue a new build. |
Tips
To run analysis after your build, place the Microsoft Security Code Analysis build
tasks after the Publish Build Artifacts step of your build. That way, your build can
finish and post results before running static analysis tools.
Always check the 'Continue on Error' option of secure development build tasks.
Even if 1 tool fails, the others can run; there are no interdependencies.
Microsoft Security Code Analysis build tasks will fail ONLY if the tool fails to run
successfully, but they will NOT fail if and when the tool identifies issues in the code.
You can configure your build to break when a tool identifies issues in the code, using the
'Post-Analysis' build task.
Some Azure DevOps build tasks are NOT supported when run via a “Release” Pipeline. This is a
limitation of Azure DevOps; they do not support tasks that publish artifacts from within a Release
pipeline.
The results log files produced by Microsoft Security Code Analysis tasks and tools can be saved by publishing them as
a post-build artifact within Azure DevOps, or to a specified file server with a path to the file share. Publishing artifacts
to the server or to a file share can be accomplished using the
Publish Security Analysis Logs build task, which is included in the Microsoft Security Code Analysis extension
(another green shield build task).
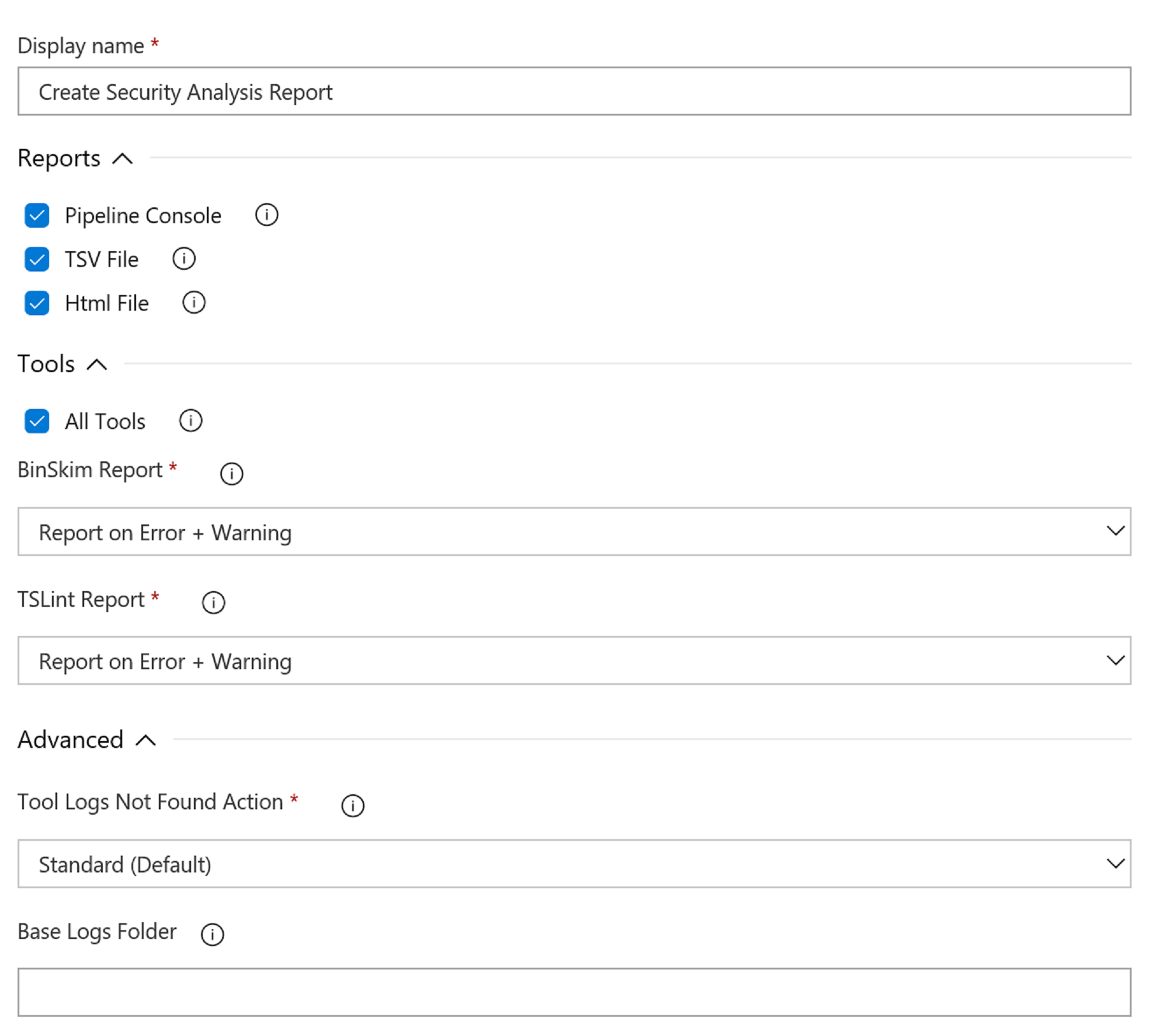
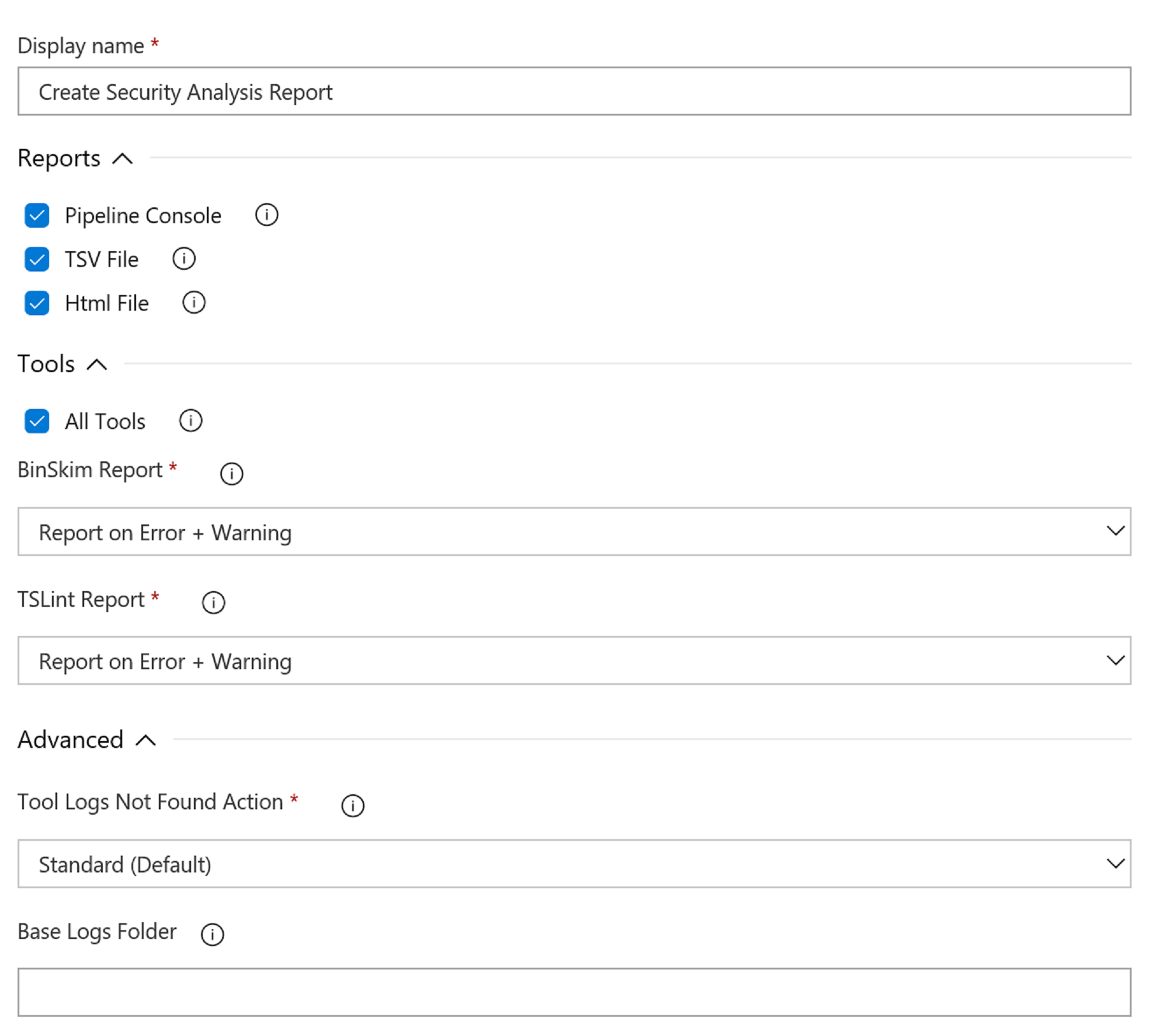
Once a build has completed, you can download the build artifacts and view the tool log files. You can also use the
Create Security Analysis Report
build task for viewing analysis result logs for specified tools, including the ability to create an actionable HTML report
file. See screenshot below for the options available in this task: