Credential Scanner (aka CredScan) is a tool developed and maintained by Microsoft to identify credential leaks such as those in source code and configuration files. Some of the commonly found types of credentials are default passwords, SQL connection strings and Certificates with private keys.
The CredScan build task is included in the Microsoft Security Code Analysis Extension. This page has the steps needed to configure & run the build task as part of your build definition.
| 1. | You are using the Azure DevOps Build system. |
|---|---|
| 2. | The Microsoft Security Code Analysis Extension installed in your account. |
| 1. | Open your team project from your Azure DevOps Account. |
|---|---|
| 2. | Navigate to the Build tab under Build and Release |
| 3. | Select the Build Definition into which you wish to add the CredScan build task.
|
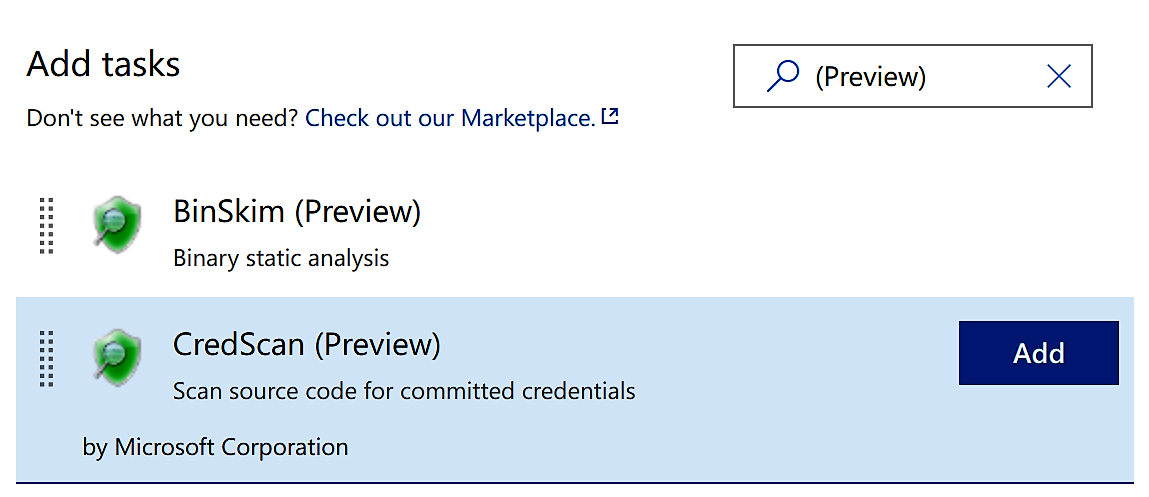
| 4. | Click + to navigate to the Add Tasks pane. |
| 5. | Find the CredScan build task either from the list or using the search box and then click
Add.
|
| 6. | The
Run CredScan build task should now be a part of the Build Definition.
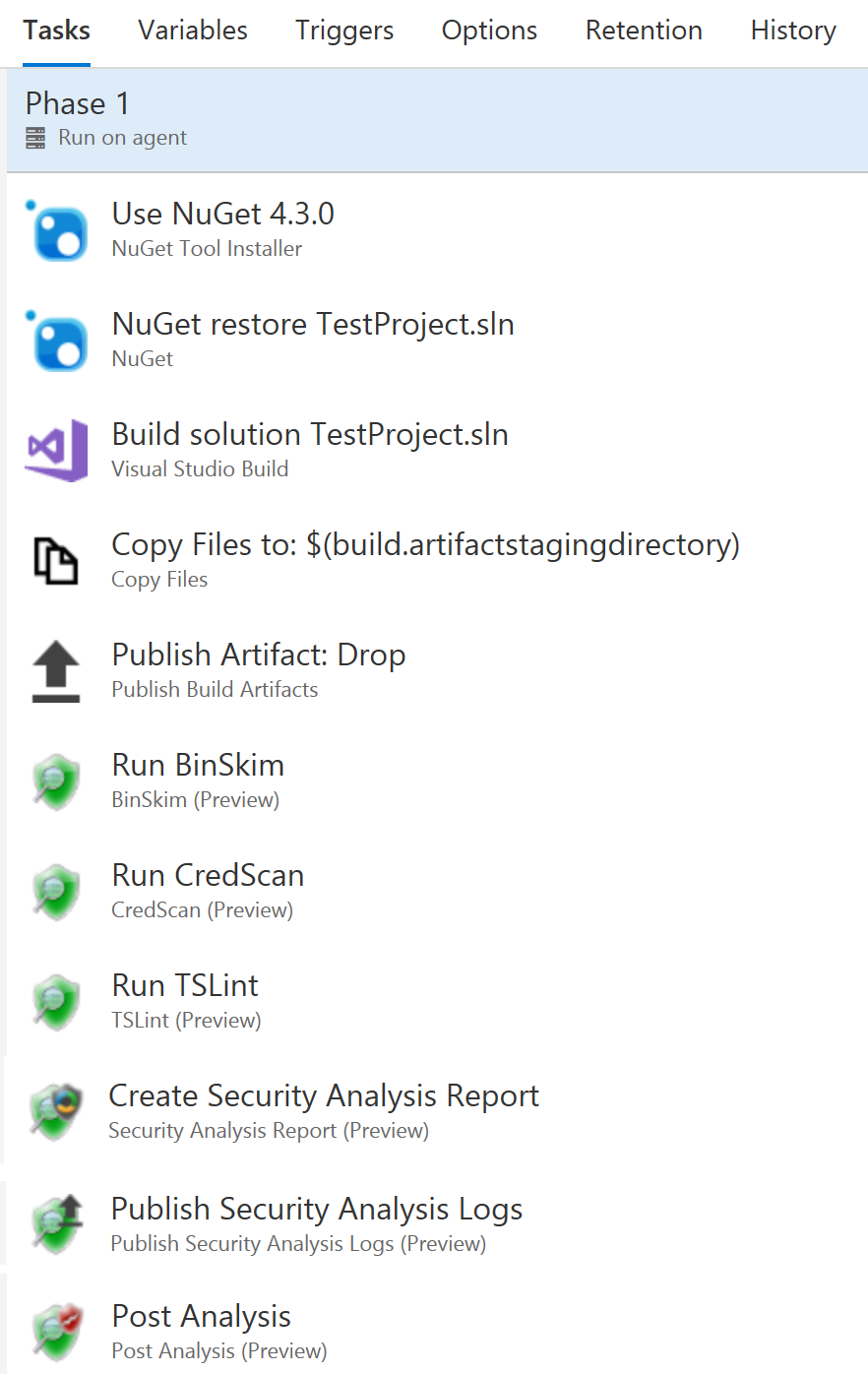
|
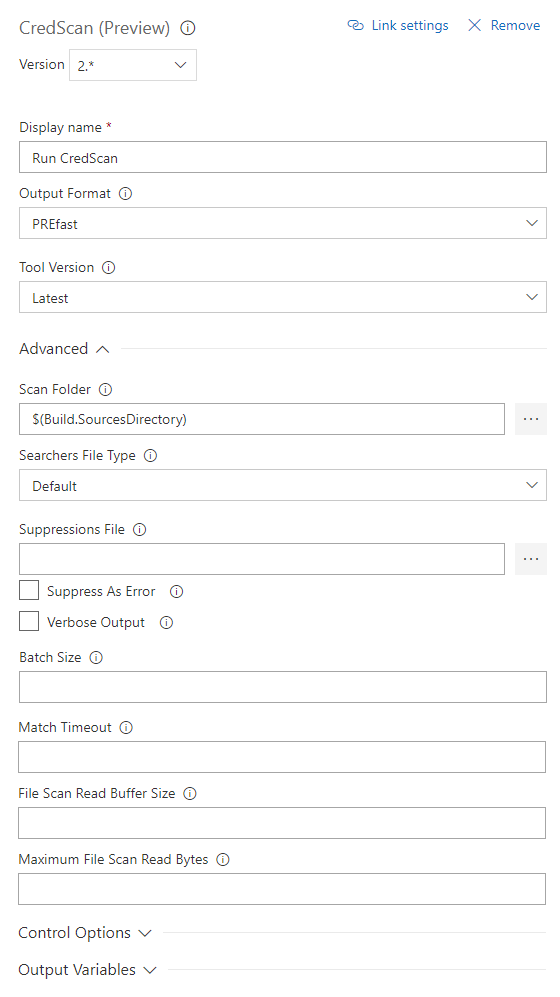
| 1. | Click the task
Run CredScan to see the different options available within.
|
|---|---|
| 2. | Available options include
*Version - Build task version within Azure DevOps. Not frequently used. |
The Private Preview for this extension is now closed. Please visit the Microsoft Security Code Analysis Home Page for information about the public MSCA extension and how to get it. You can also contact us via email at Microsoft Security Code Analysis
Two of the most common suppression scenarios are detailed below:
| 1. | Suppress all occurrences of a given secret within the specified path
The hash key of the secret from the CredScan output file is required as shown in the sample below |
|---|---|
| 2. | To suppress all secrets in a specified file (or to suppress the secrets file itself)
The file expression could be a file name or any postfix portion of the full file path/name. Wildcards are not supported.
|
While detecting hard coded secrets in a timely manner and mitigating the risks is helpful, it is even better if one could
prevent secrets from getting checked in altogether. In this regard, Microsoft has released CredScan Code Analyzer as
part of
Microsoft DevLabs extension for Visual Studio. While in early preview, it provides developers an inline experience
for detecting potential secrets in their code, giving them the opportunity to fix those issues in real-time. For more
information, please refer to
this blog on Managing Secrets Securely in the Cloud.
Below are few additional resources to help you manage secrets and access sensitive information from within your applications
in a secure manner:
CredScan relies on a set of content searchers commonly defined in the buildsearchers.xml file. The file contains an array of XML serialized objects that represent a ContentSearcher object. The program is distributed with a set of searchers that have been well tested but it does allow you to implement your own custom searchers too.
A content searcher is defined as follows:
